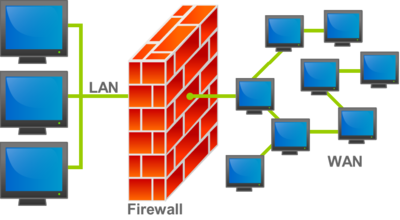
Firewall is a network security appliance that monitors incoming and outgoing network traffic and, based on a set of security rules, makes decisions to allow or block specific traffic. The firewalls have been protecting networks for more than a quarter of a century. They are a barrier between secure, controlled internal networks that can be trusted and unreliable external networks, such as the Internet. The firewall can be hardware, software, or mixed.

New Generation Firewall (NGFW)
Modern firewalls are not limited to packet filtering and session state monitoring. Most companies introduce new-generation firewalls to counter modern threats, such as sophisticated malware and application-level attacks.
A new generation firewall should have:
- standard FW functions, such as session state monitoring;
- built-in intrusion prevention system;
- accounting and control features for applications that allow you to recognize and block dangerous applications;
- update scheme to allow for future information channels;
- protection technologies against ever-changing and increasingly complex security threats.
And although these features are gradually becoming standard for most companies, new-generation firewalls are capable of more.
NGFW with Active Threat Protection
These firewalls combine the capabilities of conventional NGFW, as well as the detection and neutralization of complex threats. Firewalls of new generation with active protection against threats allow:
- determine, by taking full account of the context, which resources are most at risk;
- respond quickly to attacks with intelligent security automation, which sets policies and adjusts protection dynamically;
- detect distracting or suspicious activity with greater reliability by applying a correlation of events on the network and on end devices;
- significantly reduce the time from recognition to recovery through the use of retrospective security tools that continuously monitor suspicious activity and behavior even after the initial check;
- simplify administration and reduce complexity with unified policies that provide protection throughout the entire life cycle of an attack.