Vulnerability Management
and Penetration Testing
The best way to find out how potential intruders will break your network is to simulate an attack in the real world in a controlled environment. This approach provides a real overview of the risks your company represents from a hacker’s point of view. Rapid7 solutions can not only detect and fix detected vulnerabilities, but also exploit these vulnerabilities in a controlled environment.
1. Periodic vulnerability scans
2. Permeability test
3. Audit network policy compliance
Rapid7 Metasploit
threat penetration testing solution that allows you to evaluate risks and measures to eliminate them in order to prevent data leaks and other consequences of violating the security of your IT infrastructure
Rapid7 Metasploit allows you to track when existing vulnerabilities turn into risks as you test various ways to protect your network. Thanks to Rapid7 Metasploit, IT professionals can get a good idea of what vulnerabilities in an enterprise’s infrastructure can use malicious components to focus on the most critical and important risks.
Rapid7 Metasploit simulates an attack on a network and thus identifies its security problems, can integrate with Nexpose – a vulnerability management system – to analyze existing risks, evaluates available methods of protection against attacks and intrusion control tools, and finally determines the vulnerability to phishing and leaks confidential data (such as passwords).
Rapid7 Userinsignt
one of the most effective solutions for detecting and investigating attacks on users
Thanks to an in-depth understanding of the attacker’s mindset, Rapid7 developed UserInsight as the best security solution for detecting and investigating attacks on users inside the firewall, cloud services and mobile devices, which allows:
- Conduct a simplified study of user behavior in different environments
- Detect custom attacks based on automatic detection of abnormal behavior indicating attacks
- Quickly investigate an incident — by quickly identifying which particular user has taken an action.
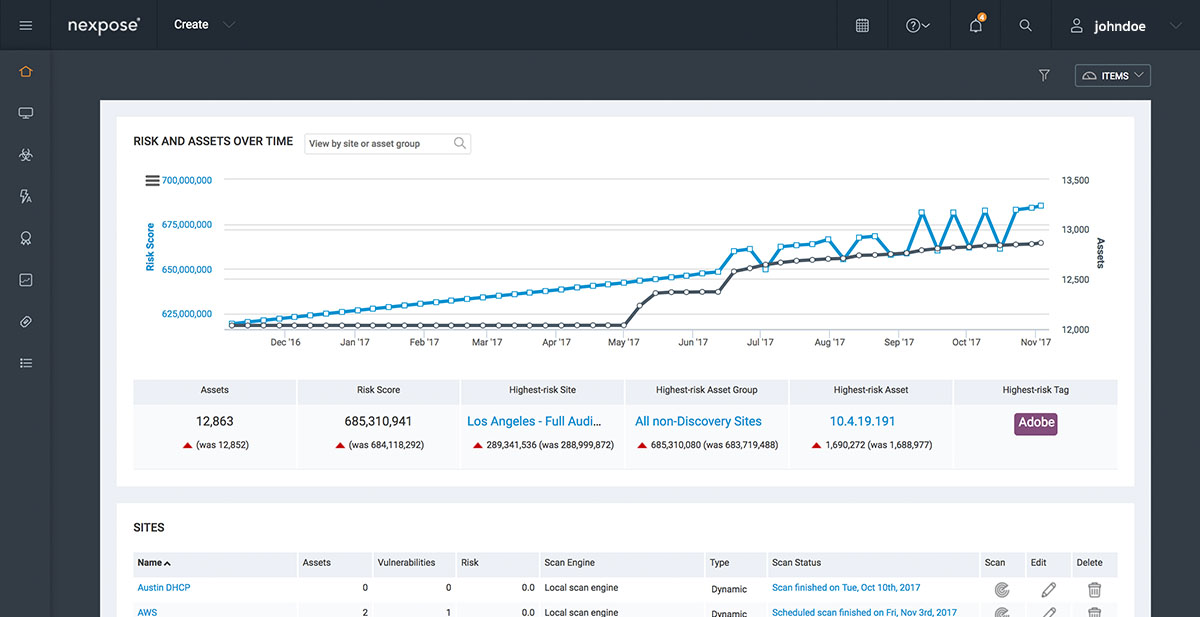
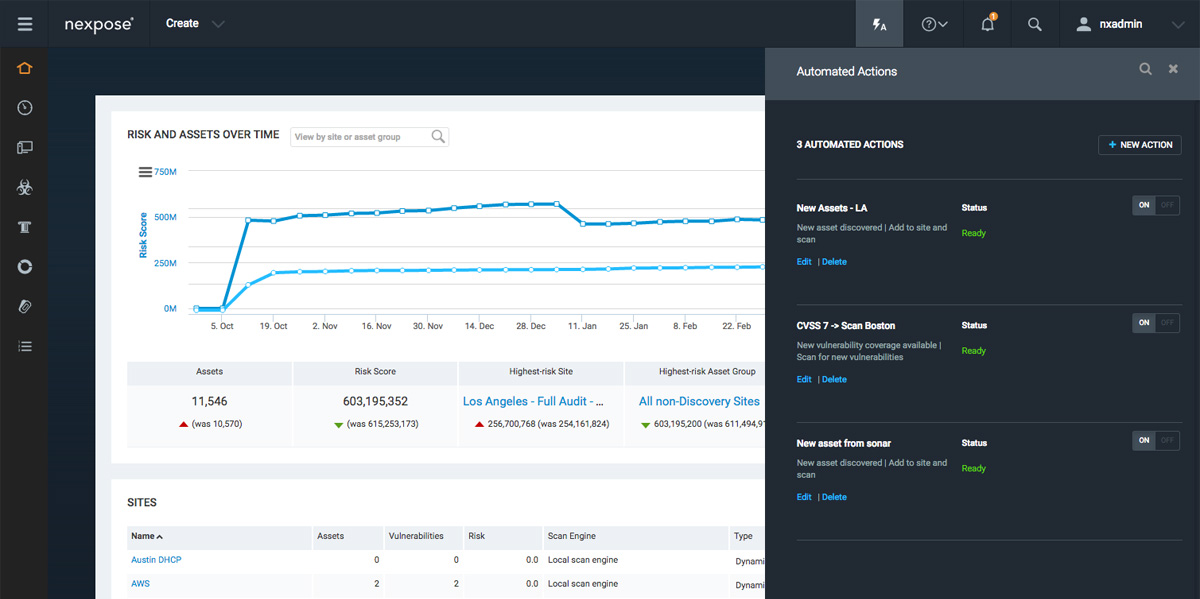
Rapid7 Nexpose
Vulnerability Management System, which performs proactive scanning of the IT infrastructure for the presence of incorrect configurations, weak points, malicious components and provides recommendations to eliminate the existing risks
Rapid7 Nexpose is a vulnerability management system that performs proactive scanning of IT infrastructure for the presence of incorrect configurations, weak points, malicious components and provides recommendations for eliminating existing risks.
Rapid7 Nexpose analyzes all infrastructure components, including networks, operating systems, databases and web applications. Following the results of the check, the application prioritizes the detected threats and generates guidelines on how to reduce each of them. The Rapid7 Nexpose system can integrate with Metasploit – a threat penetration testing solution – to comprehensively assess security risks in an organization’s IT infrastructure.
Rapid7 AppSpider
scans web applications identifying vulnerabilities and provides recommendations on recovery tools
The Rapid7 AppSpider product will help you scan all your applications for vulnerabilities, as well as provide recommendations on how to fix them.
Know your weak points
You cannot find what you cannot see. And only AppSpider will provide you with full coverage of your system by identifying all the vulnerabilities of web applications.
Prioritize the most important
Rapid7 AppSpider includes up-to-date interactive reports, and prioritizes the highest risks and urgent restoration work, which allows you to quickly eliminate and minimize risks. With a single click, you can delve into the vulnerability to get more information and reproduce the attack in real time.
Improve Your Positions
Attackers do not wait until you fix your vulnerabilities. The unique features of AppSpider allow you to automatically create targeted patches that address specific vulnerabilities in web applications.