Information Security

Information becomes one of the most valuable assets of most modern companies. The results of their own research, developed secret technologies and other corporate know-how determine the prosperity of the business, and therefore require the same careful protection as technological equipment or inventory. RCI Consulting offers a full range of proven tools for creating an effective and reliable information protection system at all levels.
PERIMETER PROTECTION
A compulsory system for protecting the network perimeter becomes an indispensable component of the competent organization of the internal network infrastructure of commercial companies or government agencies. Such a solution allows minimizing the impact of malware from external networks and is an important element of the company’s information security.
SAFETY MANAGEMENT
A set of measures for the development and implementation of a common information security management system (ISMS) for a business or non-profit organizations is a necessary component of the global management of an enterprise.
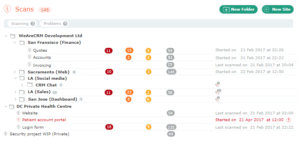
VULNERABILITY MANAGEMENT
An effective cyber security system requires constant monitoring and analysis of the weak points of corporate networks. Attackers can use these gaps to carry out attacks, so monitoring the presence of vulnerabilities in information systems and their timely elimination becomes an important task for protecting company data.
DLP
Much of the focus of information security personnel is focused on preventing and eliminating the effects of malware attacks from external sources. An equally important task is to protect the confidential information of organizations from unauthorized access, alteration, destruction or leakage as a result of employees’ actions.
ENDPOINT PROTECTION
Endpoint Security (Endpoint Security) is a client-server information security methodology designed to protect a corporate network by focusing on endpoints and analyzing (monitoring) relevant states, such as network activity, availability of a specific list of software, and proper assignment of rights. access and authentication.
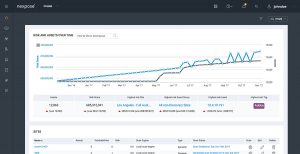
DPI
Telecom operators need reliable tools that will help to establish network monitoring of Internet traffic. Such solutions will provide a complete visualization of the network at any time.
MOBILE PROTECTION
The issues of safe operation of mobile devices when using open networks are relevant not only for individuals, but for corporate users. Companies and organizations supporting the BYOD strategy provide employees with the opportunity to use their own smartphones, tablets and similar equipment at work. Protection of mobile devices is becoming an important element of the global information security system of business and non-profit organizations.
WEB APPLICATION FIREWALL
Open web resources of your company, to which access to any Internet user is provided, need reliable protection. Potential threats to websites and other applications often result from hidden code vulnerabilities. Hackers easily use such miscalculations to obtain illegal access to various information: corporate data, personal information of customers or partners from your database. Serious damage to the business of hacking Internet applications, as a result of which the attackers gain access to the server and act on behalf of the hacked company.
What tasks solve such systems?
Loss of key data, failures in business processes and management schemes within the company, or leakage of confidential information to competitors often causes large losses. Installation of the software complex and the appropriate equipment at the site will provide protection from:
- actions of malware (viruses);
- external threats: information attacks, hacking attempts to the company’s internal computer network;
- the actions of the personnel of the enterprise, both deliberate and careless;
- equipment failures of the company: breakdowns, failure.
When planning an information security system, our engineers will take care of the convenience of the staff. Technical solutions will not affect the speed of processing customer requests and will not affect the performance of specialists. You will not have to postpone the introduction of a data protection system in order to train your colleagues on the correct use. Based on a detailed analysis of each particular enterprise, a simple scheme for controlling access to data is being developed. Employees can easily use the information they need to complete daily tasks.