Corporate-grade wireless access points are strikingly different from their home counterparts not only in hardware, but also in the presence of intelligent software. In wireless solutions for Enterprise Networks, the standard was the presence of an automatic spectrum analyzer that allows identifying the source of interference and not only changing the radio channel, but also the antenna pattern, reducing interference and orienting radiation towards the client. Thus, the wireless network provides a stable signal quality and has the property of “self-healing” without the need for regular intervention by the engineer.
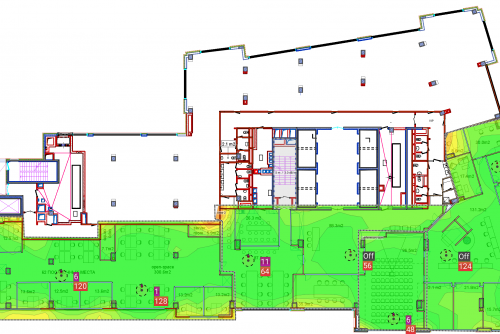
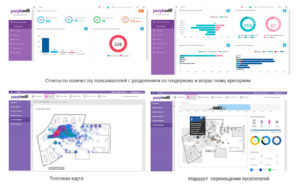
An important difference in corporate Wi-Fi is the centralization of control with the help of controllers. To cope with the simultaneous setup of several hundreds, or even thousands of wireless points, possibly remote from each other for many kilometers – the task is achievable only with the help of the controller. Otherwise, each such task will result in serious costs (labor, idle time) for the business. Such functions as the collection and visual presentation of statistics for each of the points, geolocation inside buildings, and centralized client authorization will not be redundant. A new trend for corporate networks is the removal of the controller to the computing cloud, which eliminates the need to install additional equipment and actually increases the potential expansion of the wireless network to infinity.
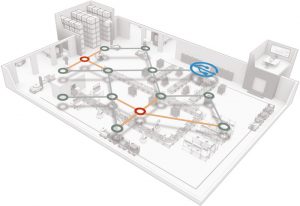
High speed in a complex radio environment, connection reliability, seamless roaming and load balancing between points on the same network are all not available to users of home access points. With impressive functionality, corporate Wi-Fi can be much easier in the initial setup, and even more in further use than home devices. Instant solutions on self-adjusting corporate Wi-Fi network, ready for full-fledged work within 5 minutes after switching on; it is enough to set the parameters for one point and it will take over the job of setting up the rest of the wireless network.


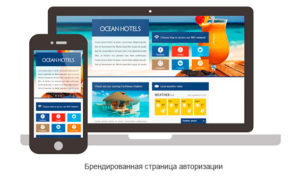
The security approach is another key advantage of the Wi-Fi enterprise sector. As you know, the password on the access point does not give a 100% guarantee against hacking the network, it can be picked up with the help of special programs, or compromised by the user’s short-sighted actions. In any case, this is the simplest, but not the safest solution (worse, just leave the wireless network completely unprotected). Corporate solutions include the possibility of not only simple authorization with a single password, but also the presence of individual passwords, flexible settings and access rights for each user, access to the network using USB keys or software certificates, continuous traffic analysis, anomaly detection, search and suppression of unauthorized wireless points.